In this demonstration, NetFoundry Senior Solutions Architect Nic Fragale highlights the inherent flaws of traditional perimeter-based security solutions, such as firewalls and VPNs. He illustrates that leaving applications visible on the internet invites automated scanning and exploitation, proving that simply relying on API authentication layers like bearer tokens is ineffective if bad actors can reach the server. Fragale then introduces NetFoundry's platform, demonstrating how closing all inbound firewall ports and utilizing an overlay network makes workloads entirely invisible to the internet. Finally, he shows how authorized users and devices are dynamically granted seamless, identity-verified access without the need to modify legacy network infrastructure.

Three Key Takeaways:
-
Legacy Security Exposes Applications: Traditional "bolt-on" security layers are complex to manage and still leave web resources visible to the internet, allowing attackers to continuously scan and probe for vulnerabilities even if API authentication layers are present.
-
Invisibility is the Ultimate Defense: By closing all inbound firewall ports and utilizing "cloaked mode," NetFoundry makes applications, APIs, and workloads completely invisible to unauthorized internet traffic, entirely eliminating the attack surface and nullifying zero-day opportunities.
-
Seamless Zero Trust Access: The platform operates on a "deny all" default state, granting end-to-end encrypted, identity-verified access to authorized users and devices in seconds, without requiring changes to firewalls, VPNs, or DNS records.
Network Exposure Demo
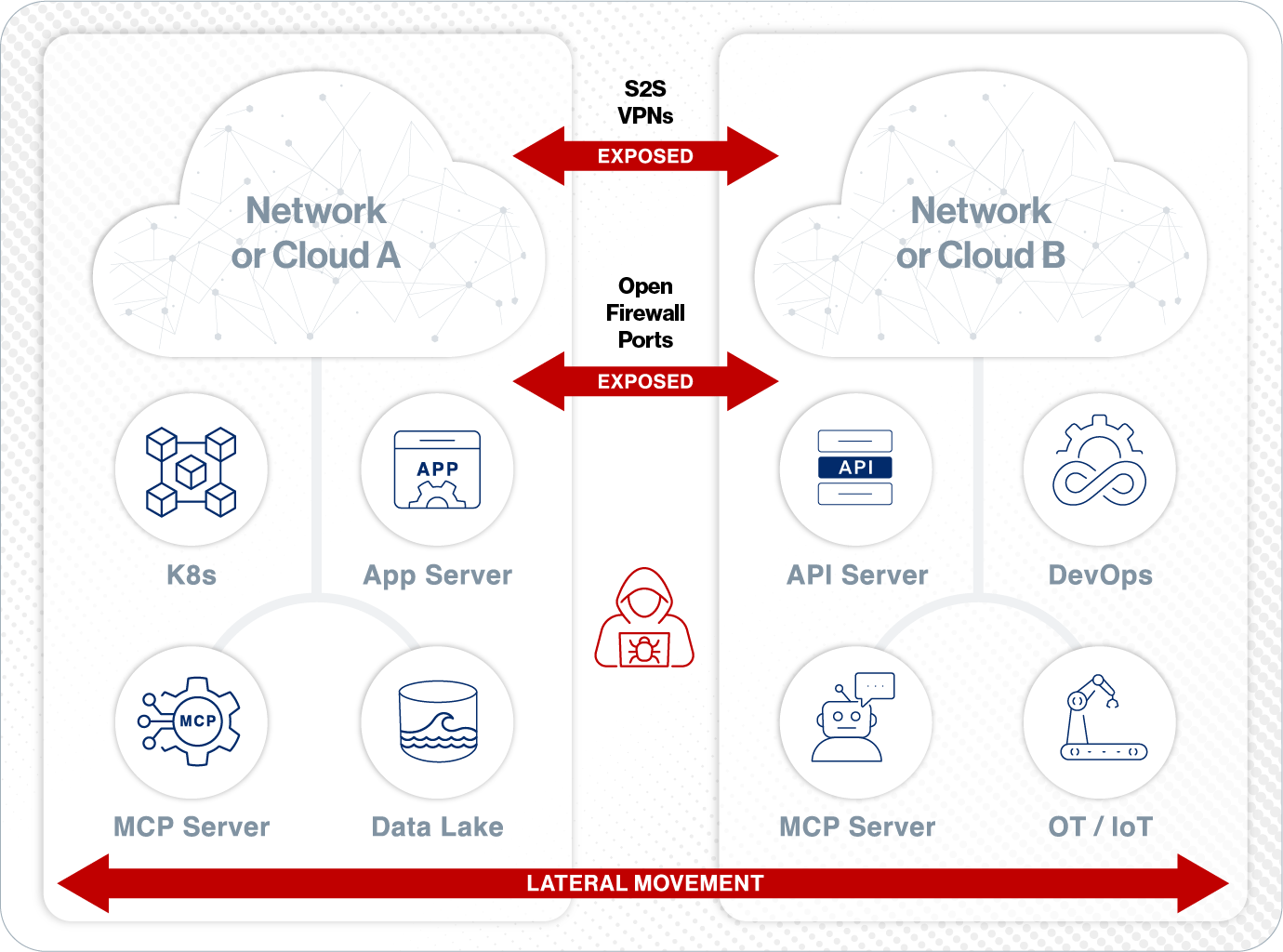
Workload Deployments Create Risk and Operational Headaches
-
Risky IP connectivity occurs before session authentication and authorization
-
Constant firewall rule changes
-
APIs exposed to entire internet
-
VPNs give excessive remote access
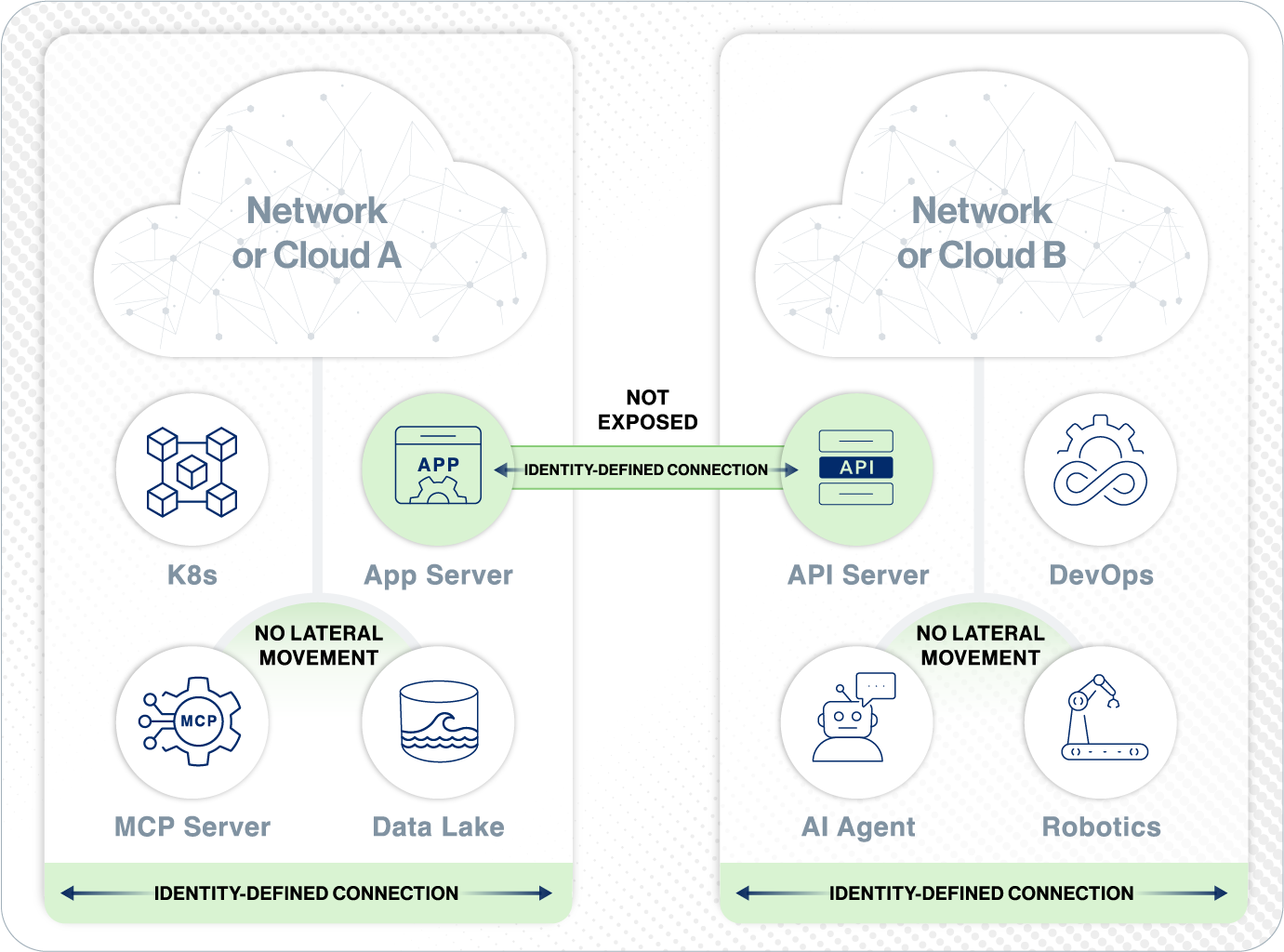
Identity-First Connectivity™
is Simple and Secure
-
All endpoints authenticated and authorized before any IP connectivity
-
Embed Zero Trust connectivity into your workloads
-
Accelerate your deployments
-
Protect your attack surface